Immortal Words – “Trust, but Verify” – No Longer Apply
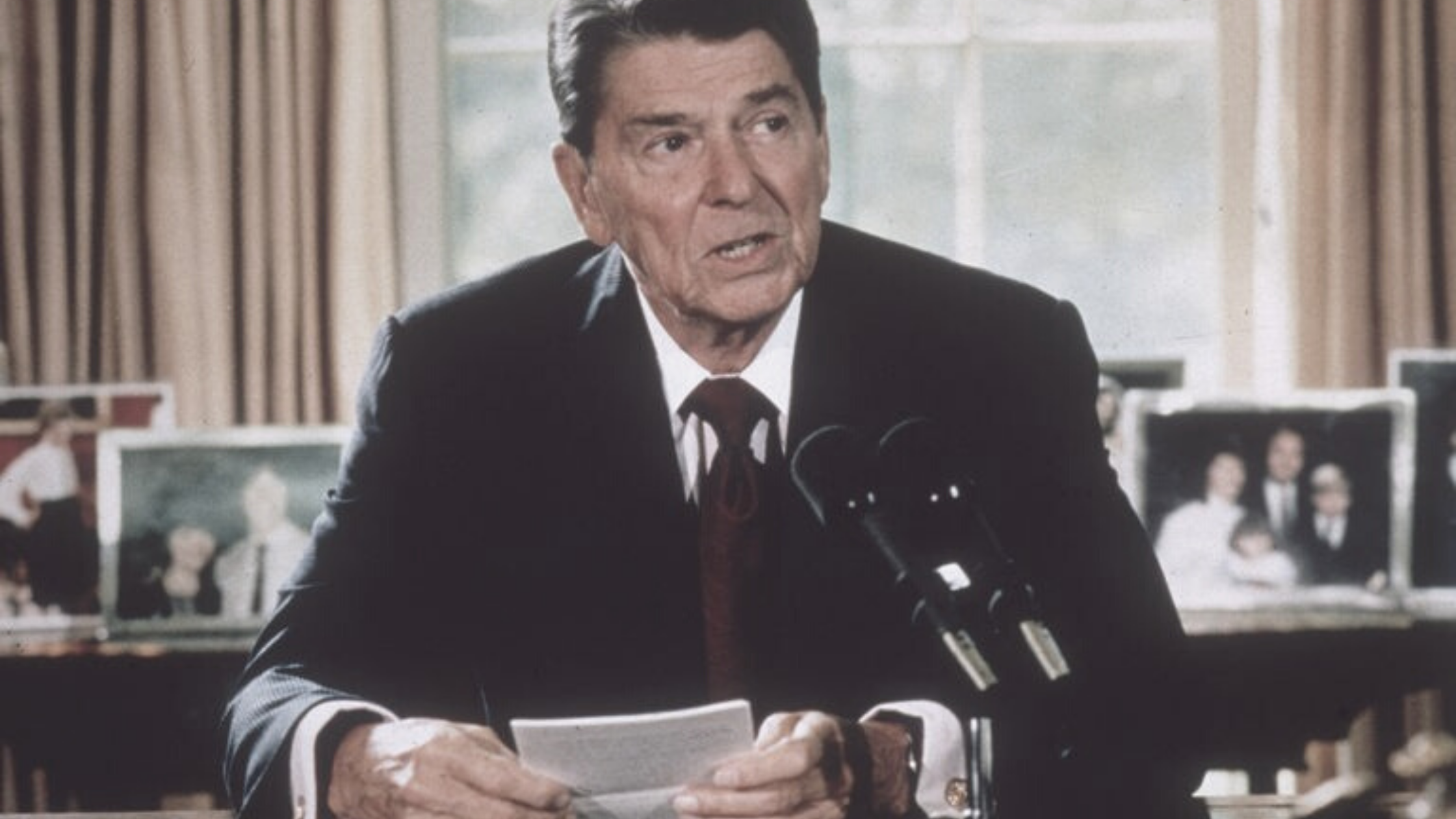
“Trust, but verify” went the famous saying from the mid-1980s when President Reagan and Soviet President Gorbachev were negotiating nuclear arms agreements.
Based on a Russian proverb, the phrase was such a favorite of Reagan’s that Gorbachev was reportedly annoyed by its repeated use. The saying essentially meant, “Sure, we’ll approach this in good faith, but we’re going to double-check to see that you’ve done what you promised.”
Fast-forward three-and-a-half decades to a world where technology and business are inextricably linked and the headline becomes, “Never trust, always verify.” The current cybersecurity/ransomware landscape being as it is, a “guilty until proven innocent” posture, is now the only reasonable approach to system access. In other words, systems will be more secure with a default policy of denying access until trustworthiness is proved, not the other way around. The question is: How did we get to this point?
In traditional security systems, people were initially verified as a part of an organization and trusted by the system from that point forward. However, this left malware with the ability to pose as an already trusted individual and slip through the cracks of the system. They were granted access to sensitive information, without ever having to face another step of verification.
Because of those detrimental errors in the system, constantly verifying everyone’s access has become the only safe way to continue. The Zero Trust system was created and implemented and became the new framework to organize and protect companies’ information. Instead of only having to pass through one layer, the Zero Trust system adds multiple checkpoints to pass through before being given access.
The “Never Trust” system is a great form of protection for a company, however, there are pitfalls. It is cumbersome for employees to have to constantly prove their legitimacy to the system, and some protocols and resources must be excluded that leave weakness. It also makes it very difficult to review and control the system because of how protected it is.
While these challenges of Zero Trust make it more difficult to maneuver, it is still a far more effective and secure system for companies to use. It is extremely successful in preventing data breaches by adding multiple layers of protection, an invaluable perk for large companies dealing with confidential information.
President Reagan would have understood today’s challenges and no doubt he would have changed his mantra. If he was negotiating with President Gorbachev in 2021, he might say in a stern voice: “Nothing personal Mr. President, but Zero Trust. Verify. Verify. Verify.”
